Lately I’ve been asked a lot why the Blockchain was created in the first place, what is its conceptual motivation. In this series of articles, I will try to explain its origins and its fundamental motivations; therefore, fasten your seat belts.
What is distrust? We can try to define it, each one with their perception, but it should not be very different from what I have found in the Cambridge Dictionary: “Believing that someone is not good or honest, and that they can hurt me”.
Let us imagine a strong mistrust, based on experience rather than suspicion. Now we apply this distrust to certain information (a contract, a work, private data, etc.); therefore, we need to protect it from someone who is certainly going to fraudulently manipulate it for their interests (criminals, authoritarian governments, unscrupulous companies, rivals, etc.).
The first characteristic that we will look for will be to protect the integrity of the content of this information. We will call it immutability. This can be achieved by preventing the information from being tampered with (signed and guarded paper) or revealing easily whether it has been tampered with (digital world).
Although this information is immutable, while still intelligible, they can use it against us. What can we do? One possibility could be to hide it. Another possibility would be not to hide it, but to transform it so that its content is unintelligible to others. That is, encrypt it.
We feel very secure, but they can still destroy and replace this immutable and encrypted information. What else can we do? A good option might be to make enough copies and distribute them to people who don’t know each other or even ignore they have it. This is the option of decentralized information.
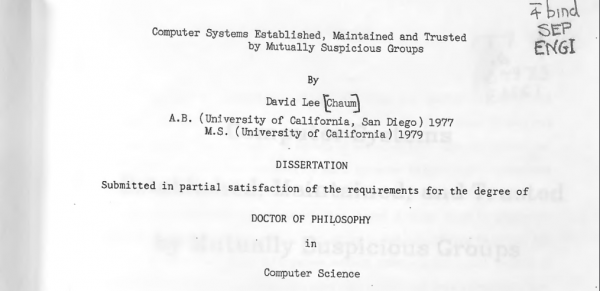
The same considerations due to distrust (immutability, encryption and decentralization), led a cryptographic mathematician at the University of Berkley, David Chaum, in 1982, to formalize a famous dissertation: “Computer Systems Established, Maintained, and Trusted by Mutually Suspicious Groups”. This dissertation is considered the birth of the Blockchain concept.
Reading the original dissertation, it is very surprising to note that most of the elements of the first Blockchain created 26 years later (Bitcoin), were already present in this very complete theoretical document. The description of this new system was so detailed that it included the programming code to implement it; To simplify, and forgive me if I am not very exact, this system consisted of connecting a series of “vaults” (safe) in a computer network, which guaranteed in the event of a malicious attack, the integrity of the data and mechanisms of self-destruction and subsequent reconstruction by authorized personnel with partial passwords.
Was David Chaum the only person with these kinds of concerns? It seems not. Have you ever heard the word Cypherpunk?
The first part of the Blockchain timeline ends here, if you want to know how this real story unfolds, stay tuned, see you in the next article.
In the meantime, have a look at the Virtual Machine for Ethereum Blockchain
The following two tabs change content below.


Mario Scalabrino
CEO at Certifydoc
Mario loves to read and write articles. He also loves to share knowledge especially if it’s likely to have social or cultural influence. Since he detests fake news, he always carefully verifies the sources of his articles.
He is enthusiastic about science, nature, dancing, partying and people, but not necessarily in that order.
A high tech entrepreneur and a forensic consultant, he holds an MSE in Electronic Engineering and a Master in Mediations and Conflicts Resolution.
He was also an International Software Sales Director and an Armed Forces Officer in Forensic Scientific Investigation.
Mario loves people who demonstrate tolerance, equality and respect for everyone.
Follow Mario on LinkedIn or on Twitter
Latest posts by Mario Scalabrino (see all)
- Multimodal transport interoperability and European strategic autonomy - 02/05/26
- Certifydoc on dual use civil-military mobility at Ferrmed annual conference - 20/11/25
- Press Release – CERT connects Vocational Education with Europe: verifiable credentials, digital identity and ESCO harmonisation - 30/10/25
- Certifydoc for ERCI Task Force on “Military Mobility” - 22/03/25
- Press release – UPC Confirms Verified Legal Value of Certifydoc’s Certifications - 08/01/25



Recent Comments